More K–12 educators are spending their own money on classroom essentials like books and other learning materials, according to a new survey. At the same time, most are not being given a say in how American Rescue Plan funds are being allocated.

Virtual education platform InSpace, a new tool that allows students and instructors to interact online much like they would in physical spaces, has announced integration with Instructure's Canvas learning management system.
Amid new fears arising over the Delta variant and wildly contradictory messaging on COVID-19 policy at all levels of government, parents appear to be growing increasingly concerned about sending their kids back to school in the fall.
A new report noted that students on the whole did make gains during the 2020–2021 school year. However, those gains were lower than seen in previous years. Underrepresented groups and students in high-poverty areas were disproportionately impacted negatively by the public policy response to the pandemic.
A new report finds that high-quality instructional materials that incorporate technology, that are culturally relevant and that bring caregivers into student learning helped remote students meet or even exceed expectations during school shutdowns.
As students return to in-person school in the fall, a science specialist explains how she’ll apply the lessons she learned during distance learning.
A survey of K–12 math and writing teachers released today found that most believe student engagement has waned during the pandemic and that student achievement has also suffered.
A survey of K–5 educators conducted this spring found that 78% of teachers had to spend their own money to supplement technology needed for teaching at home during the pandemic. The same survey found that 80% of elementary teachers spend their own money on classroom supplies.
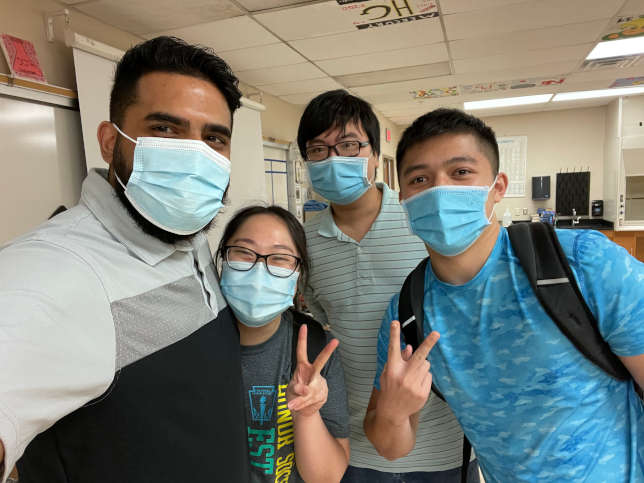
An AP chemistry teacher shares how he guides his students towards independent learning, no matter if they’re in the same room or not.
Parents and educators know that academic excellence depends considerably on students’ holistic development and a strong, positive learning environment. Unfortunately, many schools lack access to the tools needed to support students’ personal growth and to measure and reflect on their climate for learning.