
The technology behind Bitcoin has important implications for education. Here’s how.

Coding competitions drive critical thinking and help students develop workforce skills. Here’s a look inside the recent state finals for the New Hampshire Cyber Robotics Coding Competition, held at the University of New Hampshire campus in Durham.
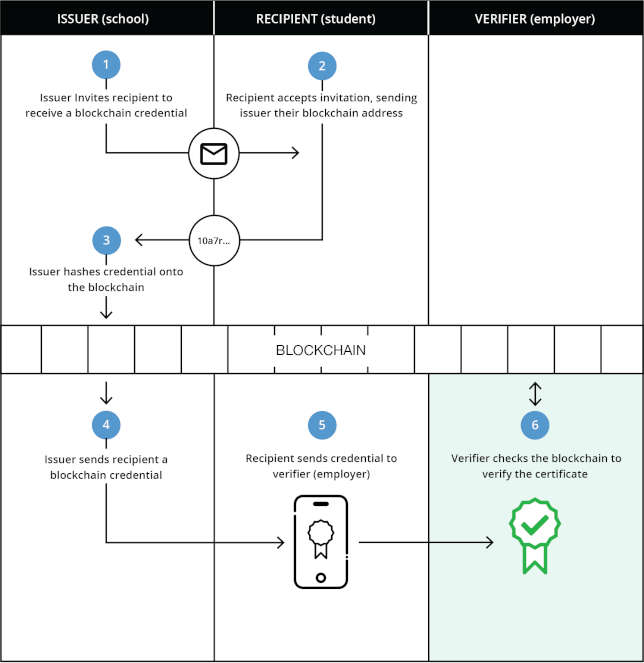
When it comes to using blockchain technology, there are several use cases across all sectors that institutions are interested in. However, some considerations need to be taken into account before jumping into the technology in full force.
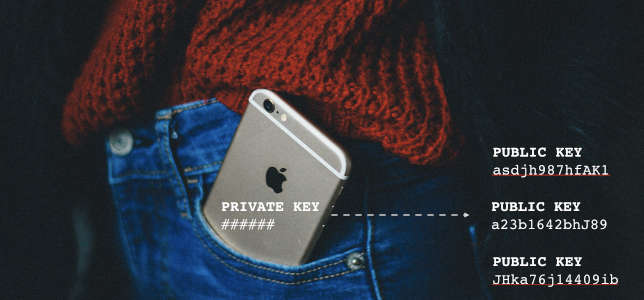
While the technology is still in the nascent stages, blockchain-based education systems have the potential to revolutionize how school districts manage student data.

This professional development opportunity helps you with the basics and even includes freely available curriculum.
At Tustin Unified School District, new teachers and their mentors use video of classroom instruction to find which areas of their practice work, and which need improvement.

Plano ISD manages a 1-to-1 environment with 52,000 Chromebooks. Here, two tech administrators share the five essential tools that make it all work.

As pedagogy evolves and classrooms move further and further away from the sage on the stage model of knowledge delivery, how can districts make sure their classrooms are supporting innovative new teaching styles?

Robotics programs across the country are appealing to non-STEM-oriented students too, even as they learn science, tech, engineering and math (along with a whole bunch of soft skills) on the side.

Five school technology leaders answer our questions on learning with tech, sustainable 1-to-1, ESSA, student data privacy concerns and what they'd give up in their jobs if only they could.